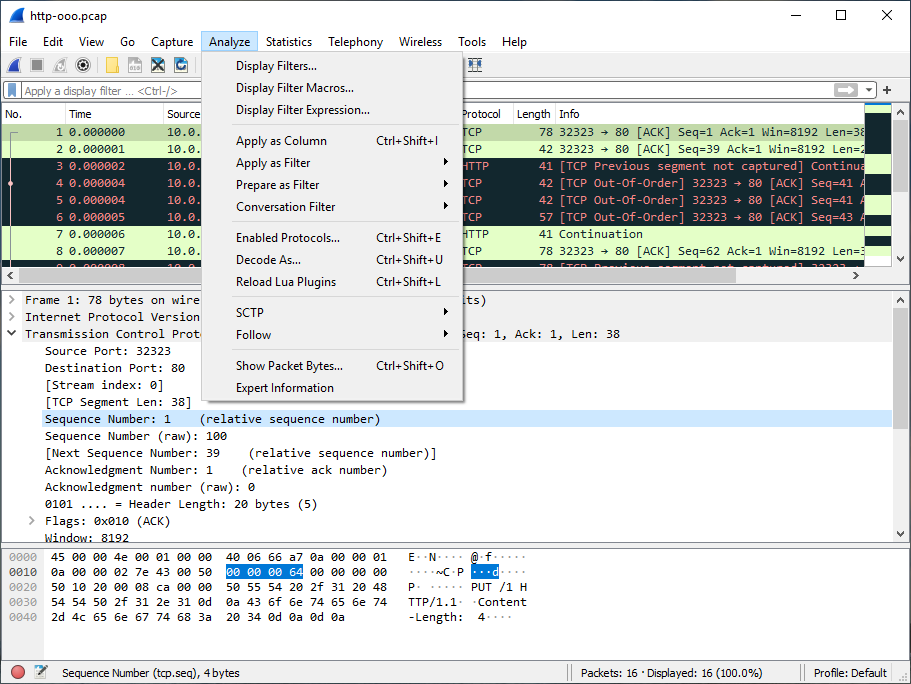
The Wireshark Analyze menu contains the fields shown in Table 3.8, “Analyze menu items”.
Table 3.8. Analyze menu items
| Menu Item | Accelerator | Description |
|---|---|---|
Displays a dialog box that allows you to create and edit display filters. You can name filters, and you can save them for future use. See Section 6.6, “Defining And Saving Filters”. | ||
Shows a dialog box that allows you to create and edit display filter macros. You can name filter macros, and you can save them for future use. See Section 6.7, “Defining And Saving Filter Macros”. | ||
Shows a dialog box that allows you to build a display filter expression to apply. This shows possible fields and their applicable relations and values, and allows you to search by name and description. See Section 6.5, “The “Display Filter Expression” Dialog Box”. | ||
Shift+Ctrl+I | Adds the selected protocol item in the packet details pane as a column to the packet list. | |
Change the current display filter and apply it immediately. Depending on the chosen menu item, the current display filter string will be replaced or appended to by the selected protocol field in the packet details pane. | ||
Change the current display filter but won’t apply it. Depending on the chosen menu item, the current display filter string will be replaced or appended to by the selected protocol field in the packet details pane. | ||
Apply a conversation filter for various protocols. | ||
Shift+Ctrl+E | Enable or disable various protocol dissectors. See Section 11.4.1, “The “Enabled Protocols” dialog box”. | |
Decode certain packets as a particular protocol. See Section 11.4.2, “User Specified Decodes”. | ||
Allows you to analyze and prepare a filter for this SCTP association. See Section 9.13, “SCTP Windows”. | ||
Opens a sub-menu with options of various types of protocol streams to follow. The entries for protocols which aren’t found in the currently selected packet will be disabled. See Section 7.2, “Following Protocol Streams”. | ||
Open a window allowing for decoding and reformatting packet bytes. You can do actions like Base64 decode, decompress, interpret as a different character encoding, interpret bytes as an image format, and save, print, or copy to the clipboard the results. See Section 7.3, “Show Packet Bytes” for more information. | ||
Open a window showing expert information found in the capture. Some protocol dissectors add packet detail items for notable or unusual behavior, such as invalid checksums or retransmissions. Those items are shown here. See Section 7.4, “Expert Information” for more information. The amount of information will vary depend on the protocol |